Table of Content
- What Are IoT Development Services?
- Understanding the IoT Architecture Stack
- Layer 1: The Perception Layer (Physical Devices)
- Layer 2: The Network and Connectivity Layer
- Layer 3: The Data Processing Layer (Edge and Cloud)
- Layer 4: The Application Layer
- IoT Communication Protocols: A Technical Deep-Dive\
- MQTT (Message Queuing Telemetry Transport)
- CoAP (Constrained Application Protocol)
- AMQP (Advanced Message Queuing Protocol)
- Protocol Selection Guide
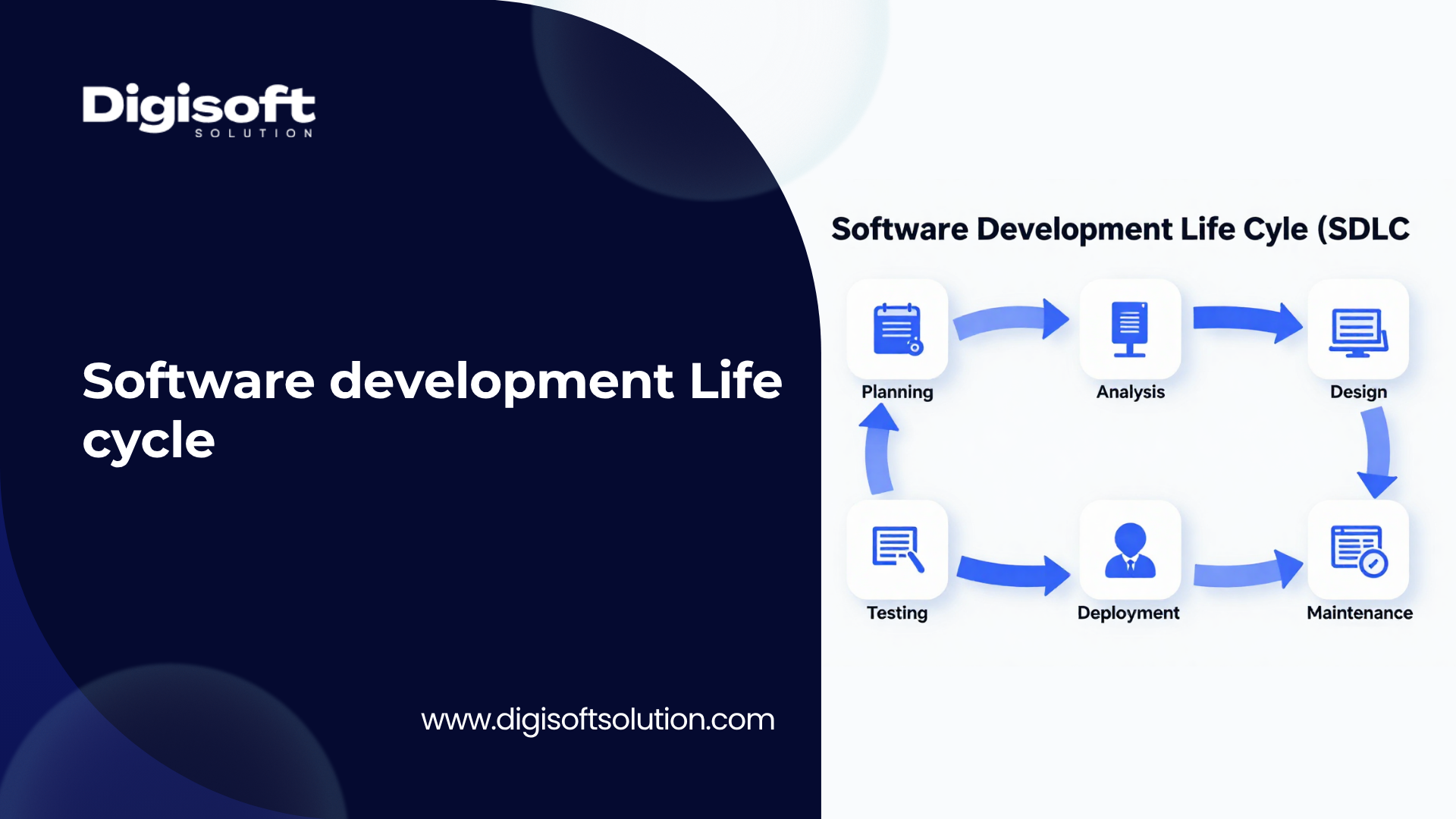
- The IoT Development Process: Phase by Phase
- Phase 1: Discovery and Requirements Engineering
- Phase 2: Hardware Selection and Prototype Design
- Phase 3: Firmware Development
- Phase 4: Cloud and Backend Development
- Phase 5: Application Development
- Phase 6: Security Hardening and Testing
- Phase 7: Deployment, Device Management, and Ongoing Support
- IoT Development Across Industries: Real Use Cases
- Manufacturing and Industrial IoT (IIoT)
- Healthcare and Medical IoT
- Smart Cities and Urban Infrastructure
- Agriculture and Precision Farming
- Retail and Consumer IoT
- Energy and Utilities
- The Real Challenges in IoT Development That Most Articles Miss
- Legacy System Integration Is Harder Than It Looks
- Network Connectivity Is Never Reliable in the Field
- Scalability Failures Are Architectural, Not Infrastructure Problems
- Security Is Still Treated as an Afterthought
- Data Quality Degrades with Scale
- Talent Gaps Are Real and Significant
- Regulatory Complexity Is Increasing
- How to Choose the Right IoT Development Partner in 2026
- Look for Full-Stack IoT Expertise, Not Application Development Experience
- Evaluate Security Design Philosophy
- Assess Architecture for Your Target Scale
- Understand Their Support and Maintenance Model
- Verify Domain Experience in Your Industry
- AIoT: The Convergence of AI and IoT in 2026
- IoT Development Costs: Setting Realistic Expectations
- Why Digisoft Solution Is Your Ideal IoT Development Partner
- What We Deliver
- Our Development Philosophy
- Industries We Serve
- Ready to Build Your IoT Solution?
- Conclusion
Digital Transform with Us
Please feel free to share your thoughts and we can discuss it over a cup of coffee.

The Internet of Things is no longer a technology experiment. In 2026, it is a core business infrastructure layer. Billions of physical devices now collect, process, and transmit data across industries ranging from manufacturing floors and hospital wards to logistics networks and smart city grids. The global IoT market is on track to reach approximately 1.3 trillion USD by 2026, with the smart cities segment alone projected to hit 312 billion USD. This pace of growth is not slowing down. Yet despite this scale, most businesses still struggle with the same recurring question: how do we actually build reliable IoT systems that work in the real world, not just in demos? This guide answers that question in full technical depth. It covers what IoT development services include, how the architecture works from device to cloud, which protocols you need to know, what the real challenges are, and how to choose a development partner who can deliver results, not just promises. Whether you are a startup exploring a connected product idea or an enterprise digitizing operations at scale, this article gives you everything you need to make informed, confident decisions about IoT development.
What Are IoT Development Services?
IoT development services refer to the full set of technical, architectural, and engineering activities required to build, deploy, and maintain connected device systems. This is not a single service. It is a layered ecosystem of capabilities that must work together as one. Missing or weakening any layer compromises the entire system. A comprehensive IoT development engagement covers the following core service areas:
- IoT Consulting and Strategy: Defining use cases, ROI modeling, technology selection, platform evaluation, and implementation roadmaps before any code is written.
- Hardware and Sensor Selection: Identifying the right microcontrollers, sensors, actuators, and communication modules that fit power, environmental, and data requirements.
- Firmware Development: Writing low-level embedded code that controls device behavior, manages power, handles sensor data, and communicates securely with backend systems.
- IoT Communication Protocol Design: Selecting and implementing the correct messaging protocol, such as MQTT, CoAP, AMQP, or HTTP, based on bandwidth, latency, and device constraints.
- Cloud Platform Integration: Connecting devices to AWS IoT Core, Microsoft Azure IoT Hub, Google Cloud IoT, or custom backends for storage, processing, and analytics.
- Edge Computing Development: Building logic that runs directly on or near devices to reduce latency, lower bandwidth consumption, and enable offline operation.
- IoT Application Development: Creating dashboards, mobile apps, and web interfaces that surface device data and controls to end users and operators.
- Data Pipeline and Analytics Engineering: Designing systems that ingest, clean, normalize, and analyze high-velocity sensor data streams in real time.
- Security Architecture: Implementing device authentication, end-to-end encryption, OTA update security, and zero trust network policies across the IoT stack.
- Device Management: Building systems for remote monitoring, OTA firmware updates, fleet provisioning, and lifecycle management across thousands or millions of endpoints.
- QA, Testing, and Certification: Validating firmware, integration points, data accuracy, load capacity, and regulatory compliance before and after deployment.
- Post-Deployment Support and Maintenance: Ongoing monitoring, incident response, firmware patching, and performance optimization throughout the system lifetime.
Each of these service areas requires specialised expertise. A team that is strong in mobile app development but lacks embedded systems experience cannot build reliable IoT systems. This is the most common reason IoT projects fail in production.
Understanding the IoT Architecture Stack
Before building any IoT system, you need to understand its architecture. Every reliable connected device solution follows a multi-layer model where data flows from the physical world through networks into processing systems and finally into applications. Getting this architecture right from day one determines whether your system scales, stays secure, and delivers accurate insights.
Layer 1: The Perception Layer (Physical Devices)
This is where IoT begins. Sensors measure real-world conditions: temperature, humidity, pressure, motion, vibration, GPS coordinates, voltage, chemical composition, and more. Actuators respond to commands to control physical outputs like motors, valves, relays, and displays. Microcontrollers and System-on-Chip modules (such as ESP32, STM32, Nordic nRF52840, or Raspberry Pi) process sensor signals and execute firmware logic.
Key architectural decisions at this layer include:
- Power management strategy: How long must the device run on battery? What sleep cycles will be used? Will the device harvest ambient energy?
- Form factor and durability: Will it operate outdoors, in high heat, in chemical environments, or in medically regulated settings?
- Processing capability: Does the device need local AI inference (Edge AI), or can it simply forward raw data to the cloud?
- Memory and storage constraints: Embedded systems often have kilobytes of RAM, which directly shapes what firmware can do.
Layer 2: The Network and Connectivity Layer
Once data is captured, it must travel. IoT connectivity is not one-size-fits-all. The right protocol depends on range, bandwidth, power consumption, and deployment environment. In 2026, five connectivity families dominate IoT deployments:
- Wi-Fi (802.11): High bandwidth and widely available infrastructure, but power-hungry. Best for stationary devices near reliable power sources.
- Bluetooth Low Energy (BLE): Short-range, low power, ideal for wearables, asset tracking, and consumer devices within 10-100 meters.
- LoRaWAN: Low power, long range (up to 15 km in open areas), very low data rates. Excellent for agriculture, smart meters, and remote infrastructure monitoring.
- Cellular (LTE-M, NB-IoT, 5G): Global coverage, high reliability, supports mobile assets. 5G now delivers latency as low as 1ms and supports up to one million devices per square kilometer, making it transformative for industrial and smart city IoT.
- Zigbee and Z-Wave: Mesh networking protocols designed for smart home and building automation with low power and self-healing network topology.
- 5G RedCap: A reduced-capability 5G variant introduced in 2026, offering a cost-effective and power-efficient middle ground for devices that need more than LTE-M but less than full 5G.
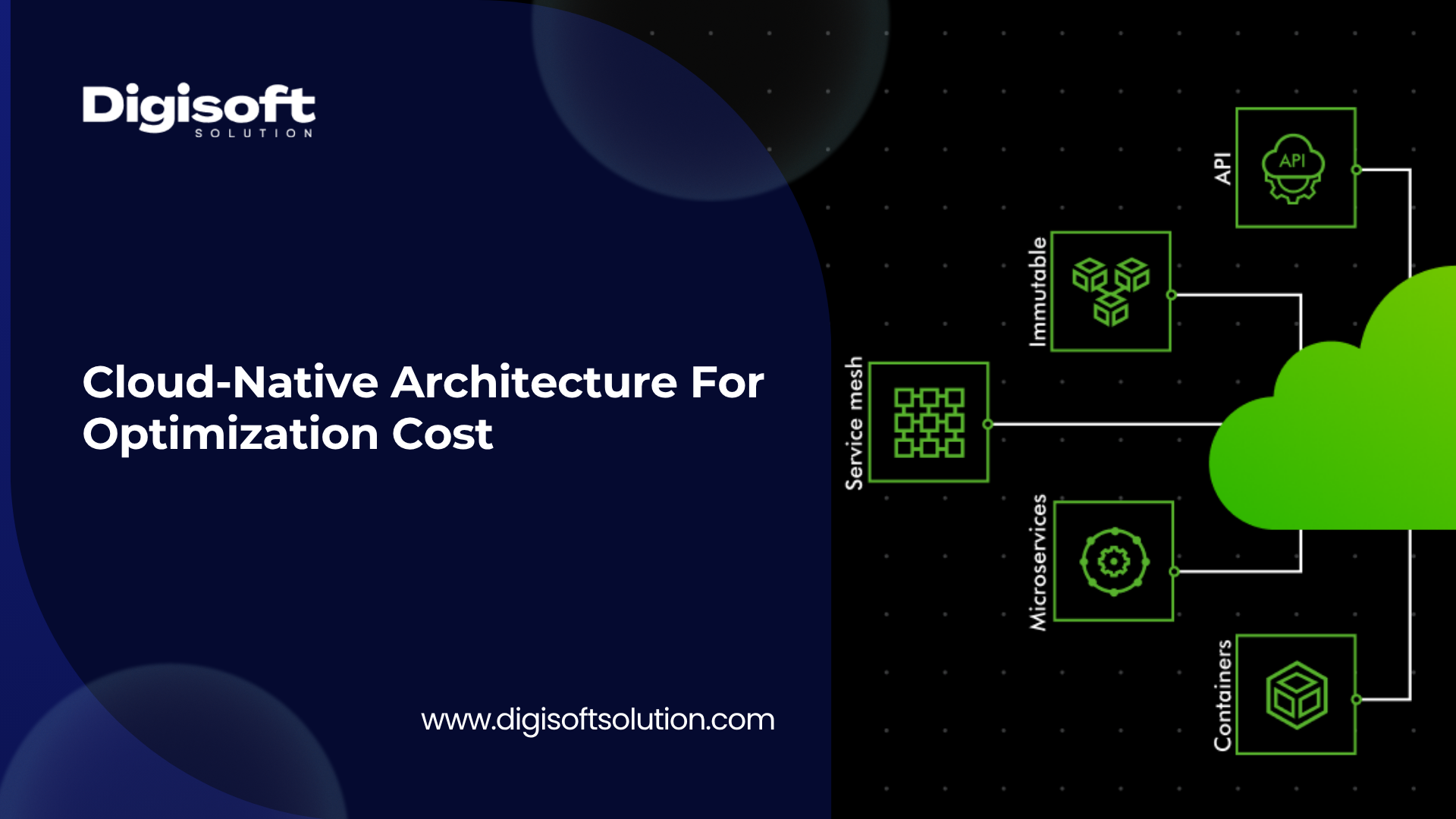
Layer 3: The Data Processing Layer (Edge and Cloud)
Raw sensor data has no business value until it is processed. In 2026, this processing happens in two complementary locations: Edge processing runs logic on or near the device. This is essential when latency requirements are tight (sub-100ms responses), connectivity is unreliable, data volumes are too large to transmit economically, or privacy regulations require local data residency. Edge AI models can run inference directly on microcontrollers using frameworks like TensorFlow Lite Micro or Edge Impulse. Cloud processing handles the heavy lifting: long-term storage, complex analytics, machine learning training, cross-device correlation, and historical reporting. In 2026, serverless architectures will become the default backend pattern. Platforms like AWS Lambda or Cloudflare Workers process device signals on demand, reducing infrastructure costs by up to 30% compared to always-on server fleets. Time-series databases such as TimescaleDB and Apache IoTDB are purpose-built for the high-frequency sensor data patterns that break traditional relational databases.
Layer 4: The Application Layer
The application layer is where IoT data becomes visible and actionable for humans and automated systems. This includes operator dashboards, mobile control applications, ERP and CRM integrations, alert and notification systems, and executive analytics portals. Importantly, the application layer must be designed for the actual users who will interact with it daily, not just for the data scientists who configured it.
IoT Communication Protocols: A Technical Deep-Dive\
Protocol selection is one of the most consequential technical decisions in IoT development. The wrong choice causes scalability failures, security vulnerabilities, and data loss. Here is what every developer and technical decision-maker needs to understand about the major IoT protocols in 2026.
MQTT (Message Queuing Telemetry Transport)
MQTT is the dominant communication protocol for IoT in 2026, powering millions of connected devices worldwide across smart homes, industrial systems, healthcare, agriculture, and transportation. Originally developed by IBM in 1999 for connecting oil pipeline sensors via satellite, it has become the de facto standard for device-to-cloud messaging. MQTT operates on a publish-subscribe model over TCP/IP. Devices publish messages to topics on a central broker. Other devices or services subscribe to those topics and receive the messages. This decoupling means publishers and subscribers never need to know about each other, which enables enormous flexibility at scale. Its technical advantages include a minimum packet overhead of just 2 bytes, efficient handling of intermittent connections through message queuing, three Quality of Service (QoS) levels to balance delivery reliability against performance, and full support for bidirectional communication. MQTT 5, the current version, adds enhanced authentication mechanisms including challenge/response authentication, native request/response patterns, detailed error reporting for better diagnostics, and improved subscription options. These additions address many of the operational pain points developers encountered with earlier versions. Security considerations with MQTT deserve careful attention. The base protocol provides minimal security beyond TCP. Communications that rely on TCP alone are unencrypted and vulnerable to man-in-the-middle attacks. Username and password fields are transmitted in clear text by default. The correct implementation uses TLS/SSL encryption, X.509 certificate-based client authentication, and careful broker configuration to prevent single points of failure. Open ports in poorly configured MQTT deployments can serve as vectors for denial-of-service attacks and buffer overflow exploits.
CoAP (Constrained Application Protocol)
CoAP is designed for extremely resource-constrained devices where even MQTT is too heavy. It runs over UDP rather than TCP, which reduces overhead significantly. CoAP is best suited for one-to-one state transfer between a client and server, making it ideal for sensors that report discrete status values rather than streaming event data. It is widely used in smart energy metering and building sensors where devices have very limited processing power.
AMQP (Advanced Message Queuing Protocol)
AMQP provides greater flexibility than MQTT but at the cost of higher protocol verbosity. For longer-lived sessions with complex routing requirements, AMQP can actually produce fewer bytes transferred overall because it amortizes the initial handshake cost across many messages. It is most commonly used in enterprise messaging systems and financial services IoT where sophisticated routing and guaranteed delivery are critical.
Protocol Selection Guide
Use the table below to match your deployment scenario to the right protocol:
|
Protocol |
Best Use Case |
Power Profile |
Range/Coverage |
Data Rate |
|
MQTT |
General IoT, real-time events, mobile assets |
Low to Medium |
Network dependent |
Variable |
|
CoAP |
Ultra-constrained sensors, state reporting |
Very Low |
Network dependent |
Very Low |
|
AMQP |
Enterprise IoT, financial systems, complex routing |
Medium to High |
Network dependent |
Medium to High |
|
BLE + MQTT |
Wearables, proximity sensing |
Very Low |
Short (10-100m) |
Low |
|
LoRaWAN |
Remote agriculture, smart meters, city sensors |
Very Low |
Long (up to 15km) |
Very Low |
|
5G + MQTT |
Industrial automation, autonomous vehicles |
Medium |
Wide area, global |
Very High |
The IoT Development Process: Phase by Phase
A well-managed IoT project follows a defined sequence of phases. Skipping or rushing any phase introduces defects that are expensive or impossible to fix after hardware is manufactured and deployed. Here is how a professional IoT development engagement actually runs.
Phase 1: Discovery and Requirements Engineering
This phase defines the entire project. Teams identify the specific use case, the business outcome being targeted, the physical environment where devices will operate, regulatory requirements, connectivity availability, and realistic ROI projections. Hardware constraints such as available memory, expected battery life, and environmental ratings are documented and validated. Early architectural decisions about edge versus cloud processing, data models, and security requirements happen here. Mistakes made in this phase cost ten times more to fix in Phase 3 than to prevent in Phase 1. A robust discovery process prevents the most common IoT failure mode: building technically functional systems that do not solve the actual business problem.
Phase 2: Hardware Selection and Prototype Design
With requirements established, the team selects sensors, microcontrollers, communication modules, and power systems. Prototype boards are assembled and tested against real-world conditions. This is where hardware-software co-design begins. Firmware and hardware must be developed in parallel, not sequentially, because hardware limitations directly constrain what software can do.
Power management is among the most underestimated challenges in this phase. A device rated for two years of battery life in a controlled lab environment may drain in three months in a cold outdoor deployment. Thermal management, moisture resistance, and connector reliability must be validated under actual deployment conditions, not assumed.
Phase 3: Firmware Development
Firmware is the low-level code embedded in the IoT device's hardware. It controls everything the device does: initializing the bootloader, reading sensor data, managing power states, establishing network connections, encrypting data, and executing OTA update procedures. Professional firmware development follows a modular architecture where hardware, firmware, and software layers are separated into self-contained modules. This makes maintenance, component replacement, and feature addition possible without rewriting entire codebases.
Critical firmware security requirements include secure boot to verify code integrity at startup, encrypted storage for credentials and keys, rollback protection to prevent downgrade attacks during OTA updates, and hardware security module (HSM) integration where sensitive operations require tamper resistance. In 2024, ONEKEY found that outdated firmware is one of the most common entry points for IoT system compromises, making this phase a security priority, not just a software delivery milestone.
Phase 4: Cloud and Backend Development
The backend receives, authenticates, processes, stores, and serves data from thousands or millions of devices simultaneously. In 2026, professional IoT backends use a serverless-first architecture for device event processing, time-series databases for sensor data storage, microservices patterns for independent scaling of different system functions, and AI-native data pipelines that extract actionable insights from raw sensor streams. IoT cloud platform selection is a long-term commitment. AWS IoT Core, Microsoft Azure IoT Hub, and specialized industrial platforms each have distinct strengths. AWS IoT Core uses a device shadow model that allows applications to interact with device state even when devices are offline, which is essential for large-scale fleet management. Azure IoT Hub excels in enterprise integration scenarios with existing Microsoft infrastructure. Platform decisions should be driven by technical requirements, not vendor relationships.
Phase 5: Application Development
End-user applications translate device data into usable interfaces. Dashboards must surface the right data to the right users with appropriate context. Alerts must be actionable. Mobile applications must work reliably on field technician devices in low-connectivity environments. This phase requires tight collaboration between UX designers, application developers, and the operations teams who will use these tools daily.
Phase 6: Security Hardening and Testing
Security cannot be added to an IoT system after it is built. It must be embedded from the firmware layer through the application layer. A zero trust approach requires that every device prove its identity before receiving any network access. Certificate-based device authentication, least-privilege access controls, network segmentation to contain compromised devices, and continuous anomaly monitoring are non-negotiable elements of any production IoT deployment in 2026.
Testing must cover not just functional correctness but load capacity at scale, failure recovery behavior, security penetration scenarios, and long-term data integrity. A system that performs well with 100 devices must be tested against the architecture it will run at 100,000 devices.
Phase 7: Deployment, Device Management, and Ongoing Support
Deployment of IoT devices is operationally complex. Provisioning thousands of devices, managing firmware update rollouts without service disruption, monitoring device health across geographically distributed fleets, and responding to field failures requires mature device management tooling and processes. OTA update capability is not optional in 2026. Security vulnerabilities discovered after deployment must be patchable remotely. Without OTA, a compromised device fleet requires physical retrieval and re-flashing, which is cost-prohibitive at any real scale.
IoT Development Across Industries: Real Use Cases
IoT delivers measurable value when it solves a specific, real-world problem with the right technical implementation. Here are the most impactful industry applications active in 2026.
Manufacturing and Industrial IoT (IIoT)
Predictive maintenance is the flagship IIoT use case. Vibration sensors, temperature monitors, and acoustic sensors attached to machinery collect continuous data streams. Machine learning models analyze these streams to detect the subtle signatures of developing mechanical failures, typically 2 to 6 weeks before visible symptoms appear. Komatsu Australia streams data from over 30,000 machines and uses IoT plus ML for predictive maintenance recommendations, achieving approximately 49 percent reduction in analytics costs and 25 to 30 percent performance improvements.
Computer vision combined with IoT sensors enables 100 percent automated defect inspection on assembly lines, replacing sampling-based quality control with continuous verification. Real-time energy monitoring tracks consumption at machine level, identifying waste that aggregate utility billing makes invisible.
Healthcare and Medical IoT
Remote patient monitoring systems continuously track vital signs, medication adherence, glucose levels, cardiac rhythms, and activity levels for patients managing chronic conditions at home. Connected inhalers record medication usage patterns and environmental conditions to help patients and clinicians identify triggers and adjust treatment. Smart hospital equipment management tracks the location and utilization of medical devices across facilities, reducing lost equipment costs and improving clinical workflow. Medical IoT operates under strict regulatory frameworks including FDA medical device requirements and HIPAA data privacy rules in the United States and equivalent frameworks globally. These requirements significantly shape architecture, certification, and testing requirements.
Smart Cities and Urban Infrastructure
Smart city IoT encompasses six major application domains: transportation management with adaptive signal control and real-time congestion detection; environmental monitoring of air quality, noise, and flood risk; utility optimization in electricity, water, and gas networks; public safety through intelligent surveillance and emergency response coordination; citizen services through digital government interfaces; and predictive infrastructure maintenance for roads, bridges, and public facilities. The global smart cities market is projected to reach 312 billion USD by 2026.
Agriculture and Precision Farming
LoRaWAN-connected soil moisture sensors, weather stations, and crop health monitors enable farmers to irrigate with precision rather than schedule, reducing water consumption significantly while improving yields. In areas with poor cellular coverage, LoRaWAN's 15-kilometer range makes connectivity economically feasible where it previously was not. Drone-based IoT systems combine aerial imaging with ground sensor data for field health mapping at scale.
Logistics and Supply Chain
Real-time asset tracking through cellular or BLE sensors, cold chain monitoring with temperature and humidity sensors for pharmaceutical and food logistics, predictive fleet maintenance, and automated warehouse systems all rely on IoT infrastructure. A poorly designed logistics IoT backend that cannot process large sensor data streams efficiently makes the system unreliable at the moment it matters most: when goods are in transit.
Retail and Consumer IoT
Smart shelf sensors track inventory in real time and trigger automatic reorder workflows. Beacon technology enables proximity-aware personalization in physical stores. Connected checkout systems reduce friction and wait times. The retail IoT market is growing at approximately 19.6 percent CAGR, reflecting how deeply embedded these systems have become in modern retail operations.
Energy and Utilities
Smart meters using MQTT transmit real-time consumption data for accurate billing and demand forecasting. Grid edge devices enable dynamic load balancing. Renewable energy monitoring tracks generation performance and predicts maintenance windows for wind turbines and solar arrays. In smart energy grids, MQTT enables real-time transmission of meter readings, ensuring accurate customer billing while giving utilities the data needed to optimize grid operations.
The Real Challenges in IoT Development That Most Articles Miss
Most IoT content covers what IoT can do. Few resources honestly address what makes IoT projects fail. Here are the genuine technical and organizational challenges that experienced IoT engineers encounter, and how to address them.
Legacy System Integration Is Harder Than It Looks
Most enterprises are not starting IoT on a greenfield. They have existing ERP systems, PLCs, SCADA systems, and operational technology networks built on protocols and architectures from the 1990s. Bridging between legacy OT systems and modern IoT platforms requires protocol translation, data normalization, security domain bridging, and careful change management. A protocol that seems ideal for a new installation may be impossible to deploy in a brownfield environment without expensive infrastructure overhaul.
Network Connectivity Is Never Reliable in the Field
IoT systems in labs have perfect Wi-Fi. IoT systems in the real world have dead zones, interference, packet loss, and cellular coverage gaps. Systems that fail to handle disconnected operation gracefully lose data, corrupt state, and require manual intervention. Every IoT system must be designed with the assumption that connectivity will be intermittent. Local buffering, store-and-forward messaging, and offline-capable firmware are architectural requirements, not optional features.
Scalability Failures Are Architectural, Not Infrastructure Problems
A system that works perfectly with 100 devices often reveals fundamental architectural weaknesses when device fleets reach 10,000 or 100,000 units. Database schemas optimized for transactional queries cannot handle millions of time-series data points per hour. MQTT broker configurations adequate for a pilot deployment become single points of failure at scale. Message queue depths grow faster than consumers can process. These are architectural problems that cannot be solved by simply adding more servers. They must be designed out before the first production deployment.
Security Is Still Treated as an Afterthought
Despite widespread awareness of IoT security risks, many IoT products still ship with hardcoded credentials, unencrypted communications, and no secure update mechanism. Cybercrime costs related to IoT breaches are projected to reach 10.5 trillion USD by 2026, with IoT devices representing a primary attack surface. The attack vectors are well understood: firmware tampering, man-in-the-middle interception, denial-of-service through open MQTT ports, physical device compromise, and supply chain attacks on hardware components. Addressing these risks requires security architecture decisions at every layer, from secure boot in firmware to zero trust access control at the network layer.
Data Quality Degrades with Scale
Raw sensor data is inherently noisy. Sensors drift over time, connectivity gaps create data holes, hardware faults produce spurious readings, and environmental conditions create outliers that look like valid data. Machine learning models fed low-quality sensor data produce unreliable predictions. IoT systems require robust data validation, anomaly detection, and quality scoring pipelines before data reaches analytics or decision-making systems.
Talent Gaps Are Real and Significant
IoT development requires expertise that spans embedded systems programming, RF communication, cloud architecture, data engineering, cybersecurity, and domain-specific knowledge of the industry being served. Finding individuals or teams with genuine depth across all of these areas is genuinely difficult. The gap between a team that can build a proof of concept and a team that can build a production-grade system is significant, and it is usually invisible until the system fails under real-world conditions.
Regulatory Complexity Is Increasing
2026 represents a watershed moment for IoT regulation. Multiple major frameworks are coming into force simultaneously. The EU Cyber Resilience Act imposes mandatory security requirements on connected product manufacturers. Industry-specific regulations in healthcare, automotive, and critical infrastructure add additional layers of compliance obligation. Regulatory compliance must be treated as an architectural requirement from the project start, not a documentation exercise at the end.
How to Choose the Right IoT Development Partner in 2026
The quality of your IoT development partner determines more about the success of your project than your budget, timeline, or technology choices. Here is a rigorous evaluation framework.
Look for Full-Stack IoT Expertise, Not Application Development Experience
Many software development companies describe themselves as IoT developers because they have built mobile applications that connect to Bluetooth devices. This is not IoT development. Genuine IoT development capability requires proven experience in firmware development, hardware selection, embedded systems constraints, communication protocol implementation, and cloud IoT platform architecture. Ask to see code. Ask to speak with engineers, not just account managers. Review practical examples, not slide decks.
Evaluate Security Design Philosophy
Ask how the team approaches device identity and authentication, firmware signing, OTA update security, network segmentation, and ongoing vulnerability management. If the answers are vague or security is described as something added at the end of the project, this is a significant warning sign. In 2026, security failures in deployed IoT systems are catastrophic and often irreversible without physical hardware recall.
Assess Architecture for Your Target Scale
Present your expected device count at initial deployment and at three-year growth projections. Ask how the proposed architecture handles that scale. Probe the answers technically. A team that designs for tomorrow's scale while delivering today's functionality is the difference between a system that becomes a bottleneck and one that enables business growth.
Understand Their Support and Maintenance Model
IoT systems require ongoing care after deployment. Firmware updates, security patches, platform version migrations, hardware end-of-life planning, and performance optimization are ongoing responsibilities. A partner who disappears after deployment delivery creates a long-term liability.
Verify Domain Experience in Your Industry
IoT in healthcare operates under different regulatory, reliability, and data handling requirements than IoT in agriculture or retail. A partner with genuine domain knowledge in your industry avoids costly mistakes that generic IoT developers make when they encounter industry-specific constraints for the first time in your project.
|
Evaluation Criterion |
What Strong Partners Do |
Warning Signs |
|
Firmware Expertise |
Show real embedded C/C++ or Rust code, discuss RTOS selection |
Talk only about app development |
|
Security Approach |
Security architecture from day one, zero trust, secure boot |
"We add security at the end" |
|
Scalability Design |
Architecture reviews at target fleet size before building |
Cannot explain how system scales |
|
Protocol Knowledge |
Explain MQTT vs CoAP tradeoffs with context |
Use a single protocol for everything |
|
OTA Management |
Rollout strategy, rollback capability, signing process |
No OTA plan for production |
|
Testing Depth |
Load testing at scale, security penetration, field simulation |
Unit tests only, no integration testing |
AIoT: The Convergence of AI and IoT in 2026
The most significant shift in IoT development in 2026 is the convergence of artificial intelligence and IoT infrastructure, increasingly referred to as AIoT. This is not just marketing language. It represents a genuine architectural transformation in how connected systems are designed and operated.
Edge AI enables intelligence to run directly on IoT devices without cloud connectivity. Modern MCUs combined with optimized neural network frameworks like TensorFlow Lite Micro execute anomaly detection, classification, and prediction locally. This enables applications that were previously impossible: real-time defect detection on a manufacturing line without sending every frame to the cloud, predictive maintenance alerts from a remote pump station with intermittent satellite connectivity, or health monitoring wearables that detect arrhythmias locally and only transmit when an event is detected.
On the cloud side, AI agents are beginning to act autonomously on IoT data streams. Rather than dashboards that humans monitor and respond to, autonomous AI systems manage supply chains, optimize energy grids, and coordinate logistics networks based on continuous real-time IoT data. This requires extremely high-quality, reliable data pipelines. An AI agent making autonomous decisions based on corrupted or delayed sensor data can cause serious operational failures. The quality of IoT data infrastructure becomes a competitive differentiator as AI autonomy increases.
Digital twins, now a standard tool in major industrial IoT deployments, create virtual replicas of physical systems that continuously synchronize with real-world sensor data. Engineers simulate failures before they occur, test configuration changes in the virtual environment before deploying them physically, and use the digital twin as a reference model for anomaly detection. In 2026, digital twins are becoming the central platform where IoT data, AI intelligence, and operational decision-making converge.
IoT Development Costs: Setting Realistic Expectations
One of the most common sources of failed IoT projects is unrealistic budget planning. IoT development is complex, and the cost components are different from traditional software projects. Here is an honest breakdown.
A proof-of-concept or pilot IoT system with limited device support and basic backend infrastructure typically falls in the range of 30,000 to 100,000 USD. This is enough to validate a concept and demonstrate technical feasibility but not enough to build a production-grade system.
A full production IoT system with robust security, scalable backend architecture, device management capabilities, and complete application layers typically ranges from 150,000 USD to 500,000 USD or more depending on complexity, device count, industry regulation requirements, and integration depth.
Several factors push costs higher than teams initially anticipate:
- Hardware certification costs: FCC, CE, UL, and industry-specific certifications are required before products can ship. These are fixed costs that do not scale with project scope.
- Security architecture: Proper device authentication, certificate management infrastructure, and OTA security mechanisms require dedicated engineering effort that cannot be eliminated without accepting serious risk.
- Testing at scale: Load testing, security penetration testing, and field simulation add cost but prevent failures that cost far more after deployment.
- Integration complexity: Connecting IoT systems to existing ERP, MES, CRM, or analytics platforms requires careful API design, data mapping, and change management.
- Ongoing operational costs: Cloud infrastructure, device connectivity data plans, monitoring services, and maintenance engineering are recurring costs that must be budgeted separately from development.
The highest-ROI IoT investments consistently come from projects with clear, specific problem definitions, realistic timelines, appropriate security budgets, and experienced partners who design for production-scale from day one rather than optimizing for demo performance.
Partner With Digisoft Solution for World-Class IoT Development
Why Digisoft Solution Is Your Ideal IoT Development Partner
Digisoft Solution builds IoT systems that work in the real world, not just in controlled demos. From embedded firmware to scalable cloud backends, we deliver connected device solutions that are secure, reliable, and built for growth.
At Digisoft Solution, we understand that IoT is not a software project with a few hardware considerations bolted on. It is a complex, multi-discipline engineering challenge that requires deep expertise at every layer of the stack. We bring that expertise, and we bring it in a way that is aligned with your business goals, not just technical deliverables.
What We Deliver
- End-to-End IoT Development: From hardware selection and firmware engineering through cloud platform architecture and end-user application development, we handle the full stack so you never have to coordinate between multiple vendors for a single product.
- Custom Firmware Engineering: Our embedded systems engineers write secure, efficient firmware for a wide range of microcontroller platforms. We implement secure boot, OTA update mechanisms, power optimization, and modular architecture from the project's start.
- Protocol Expertise: We implement MQTT, CoAP, AMQP, BLE, LoRaWAN, and 5G-based connectivity based on what your deployment actually requires, not what is easiest to implement.
- Security-First Architecture: Every system we build includes certificate-based device authentication, end-to-end encryption, zero trust network access, and a production-ready OTA update pipeline with rollback capability.
- Cloud Platform Integration: We work across AWS IoT Core, Microsoft Azure IoT Hub, and custom backend architectures, selecting the platform that matches your scale, compliance requirements, and existing infrastructure.
- Edge AI Development: We implement on-device inference for applications requiring real-time local intelligence, combining embedded machine learning with cloud analytics for the optimal performance and cost profile.
- Device Management at Scale: Our device management solutions handle fleet provisioning, OTA update rollouts, remote monitoring, and lifecycle management for deployments ranging from hundreds to hundreds of thousands of devices.
- Industry-Specific Compliance: We have experience with regulatory requirements in healthcare, manufacturing, energy, and logistics, including FDA, HIPAA, IEC 62304, and EU Cyber Resilience Act compliance considerations.
Our Development Philosophy
We design for your three-year scale on day one. A system that works perfectly at 100 devices and fails at 10,000 is not a success. We conduct architecture reviews against your projected growth targets before writing the first line of code. This prevents the expensive architectural rewrites that plague IoT projects built by teams optimizing for demo success rather than production reliability.
We treat security as a foundational requirement, not a checkbox. Our security architecture is embedded from firmware to application layer, including threat modeling, penetration testing, and ongoing vulnerability management as part of our engagement.
We communicate in business outcomes, not just technical milestones. Every phase of our development process ties technical deliverables to the measurable business results you engaged us to produce.
Industries We Serve
- Manufacturing and Industrial Automation
- Healthcare and Medical Device
- Smart Cities and Public Infrastructure
- Agriculture and Environmental Monitoring
- Logistics and Supply Chain
- Retail and Consumer Products
- Energy and Utilities
- Building Automation and Smart Facilities
Ready to Build Your IoT Solution?
If you are planning an IoT initiative, evaluating vendors, or struggling with an existing system that is not delivering what it promised, we want to talk. Digisoft Solution offers a no-obligation technical consultation where we review your requirements, identify risks, and outline a realistic path to a production-grade IoT system.
Contact us today. Building connected systems is our specialization. Your problem is exactly what we are here to solve with a free consultation.
Conclusion
The Internet of Things has crossed the threshold from emerging technology to core business infrastructure. In 2026, the question is no longer whether IoT can deliver value. It is whether your organization has the right technical foundation and the right partners to capture that value reliably and at scale.
The businesses that win with IoT in 2026 share three characteristics: they define specific, measurable problems before selecting technology; they invest in architecture and security from the beginning rather than retrofitting them later; and they partner with teams that have genuine depth across the full IoT stack, from firmware to cloud to application.
The IoT landscape is more capable than it has ever been. 5G RedCap brings enterprise-grade connectivity to more device classes. Edge AI enables intelligence at the sensor level. Digital twins provide unprecedented operational visibility. AIoT is beginning to automate decisions that previously required human monitoring. These capabilities are real and available today.
The gap between organizations that capture these capabilities and those that attempt IoT projects without adequate technical foundation and experienced partners is widening. Choosing the right IoT development partner, understanding the full technical stack, and designing for production scale from day one are the decisions that separate successful deployments from expensive lessons.
Digisoft Solution is ready to be your IoT development partner. From the first technical consultation through long-term system support, we are with you at every layer of the stack. Visit www.digisoftsolution.com to start the conversation.
Digital Transform with Us
Please feel free to share your thoughts and we can discuss it over a cup of coffee.


































































































































































 Kapil Sharma
Kapil Sharma